In my tutorial on how to block IP cameras from accessing the Internet, I used the example of wireless security cameras.
But what if you have wired IP cameras and want to achieve the same result – block PoE IP cameras from accessing the Internet? Fear not, all you need to have is any one of the following:
- [easyazon_link identifier=”B086967C9X” locale=”US” tag=”vueville.com-eaz-20″]Unifi Dream Machine Pro (UDM Pro)[/easyazon_link] which is an all-in-one device that combines a managed switch and hardware firewall, OR
- a Unifi managed switch and separate firewall, such as the [easyazon_link identifier=”B01MU3WUX1″ locale=”US” tag=”vueville.com-eaz-20″]Unifi Switch 8[/easyazon_link] & [easyazon_link identifier=”B00LV8YZLK” locale=”US” tag=”vueville.com-eaz-20″]Unifi USG firewall[/easyazon_link] combo.
Assuming you have already created a VLAN as described in Step 1 of this tutorial, here are the steps to group or assign wired Ethernet devices into a VLAN:
Step 1: Create a switch port profile
- Log into your Unifi Controller dashboard and click on the settings button (gear icon)
- From the settings menu, select ‘Profiles’, and then select the ‘Switch Ports’ tab

- Click ‘Add New Port Profile’
- Type in a profile name, I like to use the same name as the VLAN created ‘IPCameras’.
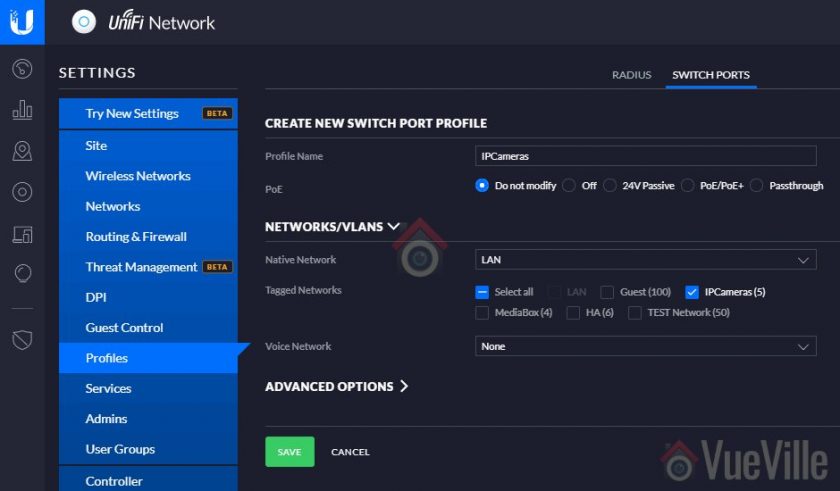
- Select the VLAN under the Tagged Networks section.
- Click Save
Step 2: Plug in your Ethernet device
Into a port of your Unifi managed switch, and note the port number. Let’s assume it is a PoE device, so let’s pick port 6.
Step 3: Assign Unifi switch port to the new switch port profile
- From your Unifi Controller dashboard and click on the Devices button from the left menu
- Click on your Unifi Switch, this should open a slide-out menu on the right


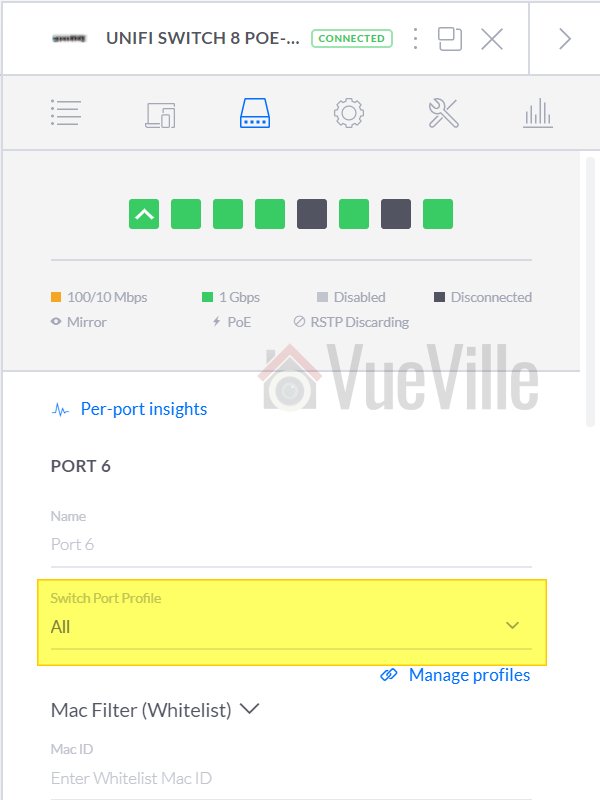
- Click on the Ports section

- Click on the edit button (pencil icon) next to port 6

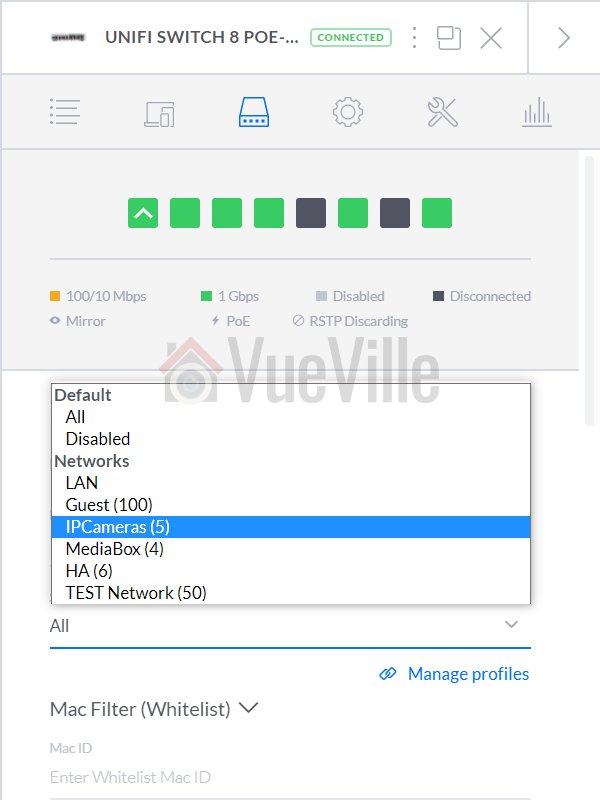
- Click the dropdown called ‘Switch Port Profile’
- Select the switch port profile you created earlier and click the apply button.
The switch will now provision the port and after a few minutes, you are in business!
How to group multiple ports into the same VLAN
Simple – just apply the port profile you created in Step 1 above to each port that you want to be in the same VLAN.
Conclusion
Liked this tutorial? Let me know in the comments below what else you would like me to cover.





Thanks for the really excellent “written” article. Unfortunately, in YouTube times, you don’t find many such detailed and thought-out “how to” instructions anymore.
Thanks for the encouragement!
my v-lan has a different IP range than my LAN. the IPCAMERAS is 192.168.2.X. Normal lan is 192.168.1.X. When I switch the port over to the new port profile, everything looks cool but the cameras are retaining their IP address(es) of 192.168.1.X. How do I get them to move over to the ‘2’?
The cameras should automatically pick up the new address system from the DNS server – have you entered the DNS settings for the VLAN correctly? You an check by connecting a laptop to that VLAN and checking what IP address is being assigned. Another thing to check is whether the cameras are on static IPs and locked into 192.168.1.X? If so, change them over to DHCP.
HI, i plan to follow your setup, may i check if i can substitute the usg, cloud key and managed switch with Unify Dream pro machine please. Will buy Hikvision cameras and QNAP 253de.
Thanks,
Arnold
I am not sure the Dream Pro machine supports all the advanced features that the USG does. You will have to check with Unifi please.
Hugely helpful, between this and your other tutorial about securing cameras! One thing I’m not clear on – is the switch port profile necessary if you want that switch port to be only on the VLAN? My version of the controller doesn’t allow the same name to be used for both VLAN creation as well as port profile creation as yours seems to, and when I apply the port profile to a port (which doesn’t look like how yours looks above, it shows up under a heading called “Custom”, below networks) the device still remains using the same IP as the untagged LAN. However, when I select the VLAN itself (as you appear to above), it all works fine, but that seems to skip the port profile creation entirely. I’m pretty green, so is there something I’m missing?
> One thing I’m not clear on – is the switch port profile necessary if you want that switch port to be only on the VLAN?
Yes the port profile is used to tag all traffic through a port with the VLAN assigned to that port profile.
> However, when I select the VLAN itself (as you appear to above), it all works fine, but that seems to skip the port profile creation entirely.
Maybe you are on a newer or older controller version? As long as your rules are being applied to the , I think you’re fine.